TrickMo Android Malware Uses TON for Stealth Attacks
A newly identified version of the TrickMo Android banking malware has emerged with expanded capabilities and a stealth-focused communication system that leverages The Open Network (TON). Cybersecurity researchers revealed that the updated malware strain is targeting Android users across several European countries, including France, Italy, and Austria, while focusing on banking credentials and cryptocurrency wallet information.
The malware, tracked as Trickmo.C by cybersecurity firm ThreatFabric, has reportedly been under observation since January. Researchers noted that the latest version disguises itself as popular applications such as TikTok clones and streaming services in an effort to trick users into installing infected software on their devices.
TON Integration Makes Detection More Difficult
One of the most significant developments in the new TrickMo variant is its adoption of TON-based command-and-control communications. Researchers explained that the malware uses.ADNL addresses are routed through a local TON proxy embedded directly on infected devices. This approach allows operators to conceal the real location of their infrastructure and avoid traditional tracking methods.
TON, originally associated with the Telegram ecosystem, functions as a decentralized peer-to-peer network that enables encrypted communication through an overlay network rather than relying on publicly exposed servers. Instead of standard domains, TON utilizes 256-bit identifiers, making it substantially harder for investigators and security teams to identify, block, or dismantle malicious infrastructure.
The latest TrickMo variant integrates TON-based command-and-control communication, significantly improving its ability to evade detection and resist infrastructure takedowns.
ThreatFabric researchers explained that traditional domain-based disruption methods become largely ineffective because the malware operators do not depend on the public DNS system. Instead, communications remain hidden within TON’s encrypted network traffic, which appears similar to regular TON-enabled application activity.
Malware Gains Expanded Offensive Capabilities
TrickMo was initially discovered in September 2019 and has remained in continuous development ever since. Previous investigations by cybersecurity company Zimperium in October 2024 identified dozens of malware variants delivered through multiple droppers and linked to numerous command-and-control infrastructures worldwide.
The malware operates through a modular two-stage architecture. The first stage consists of a host APK responsible for loading the malware and maintaining persistence on the infected device. The second stage downloads additional modules that carry out malicious operations.
The banking trojan is capable of stealing sensitive information through phishing overlays, keylogging, screen recording, live screen streaming, SMS interception, and clipboard manipulation. It can also suppress one-time password notifications, filter device notifications, and capture screenshots, giving attackers extensive control over compromised devices.
The latest version introduces several additional commands and networking features, including DNS lookup, ping execution, telnet access, traceroute functionality, SSH tunneling, remote and local port forwarding, as well as authenticated SOCKS5 proxy support.
The newly added networking and tunneling functions provide attackers with enhanced remote access and greater flexibility for maintaining covert operations on infected Android devices.
Researchers also identified traces of the Pine runtime hooking framework, previously used for intercepting networking and Firebase-related operations. However, no active hooks were found during the latest analysis. Additionally, the malware requests extensive NFC-related permissions and reports NFC capabilities back to operators, although researchers did not observe any currently active NFC exploitation features.
Android Users Urged to Exercise Caution
Cybersecurity experts continue to warn Android users against downloading applications from unofficial sources. Security professionals recommended limiting installed applications, relying only on reputable publishers, and ensuring that Google Play Protect remains enabled at all times.
Researchers warned that malware campaigns disguised as trusted entertainment and social media applications continue to pose a growing threat to banking and cryptocurrency users worldwide.
As mobile banking and digital asset adoption continue expanding globally, advanced malware operations such as TrickMo highlight the increasing sophistication of cybercriminal tactics targeting financial data and cryptocurrency holdings.
The post TrickMo Android Malware Uses TON for Stealth Attacks appeared first on CoinTrust.
You May Also Like

Best Music AI Websites For Songs And Soundtracks
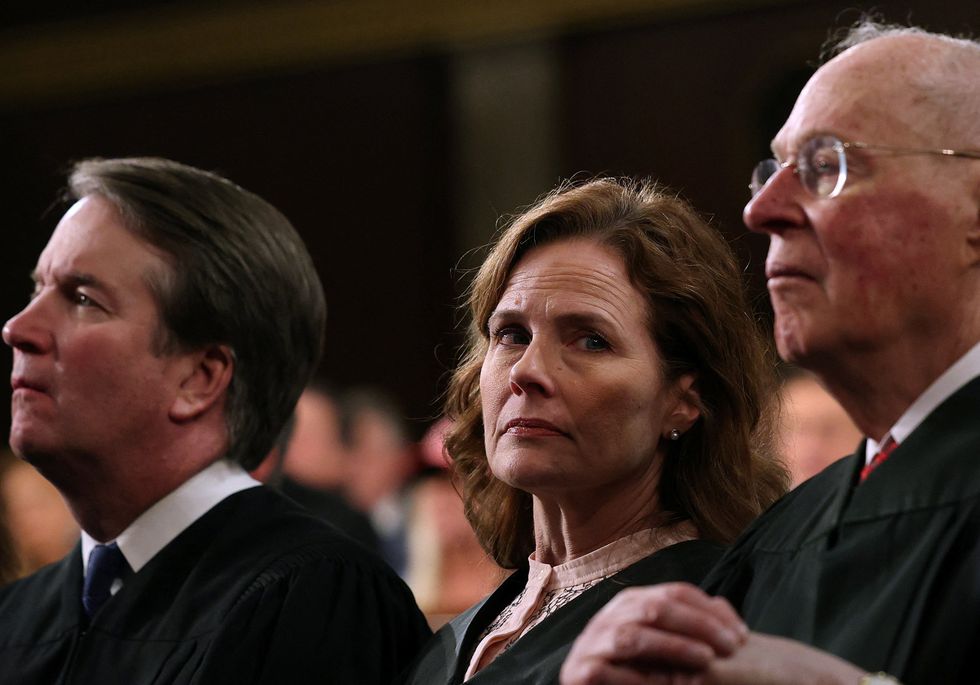
Justice’s own words prove Supreme Court 'a bunch of partisan hacks': legal scholar






