Kaspersky Uncovers Google Tasks Phishing To Steal Credentials
Editor’s note: The following briefing outlines a new phishing campaign uncovered by Kaspersky that hijacks legitimate Google Tasks notifications to steal corporate credentials. The attackers impersonate trusted services, leveraging the @google.com domain and intra-company cues to evade standard filters and pressure users into acting quickly. Victims are invited to click a link and complete a fraudulent employee verification form, exposing sensitive credentials that could grant unauthorized access. This advisory highlights the evolving tactics criminals use to exploit familiar tools and the importance of vigilance in enterprise environments.
Key points
- Attackers abuse legitimate Google Tasks notifications to steal corporate credentials.
- The campaign uses the trusted @google.com domain to bypass filters and build trust.
- Users are directed to a fraudulent employee verification form after clicking a link.
- The social engineering hinges on urgency and internal process appearance to lower defenses.
Why this matters
By exploiting familiar services, the campaign exploits trust in everyday tools, increasing the likelihood that employees reveal credentials. This approach bypasses many security filters and highlights the need for awareness and layered defenses in organizations. The incident underscores why training, MFA, and robust verification processes are critical as attackers continue to adapt to legitimate platforms.
What to watch next
- Look for more phishing attempts that imitate enterprise tools via trusted notification channels.
- Watch for fraudulent forms asking for corporate credentials and verify URLs before interacting.
- Ensure MFA and mail-server security measures are in place to protect accounts.
- Report suspicious activity to IT and update security policies as needed.
Disclosure: The content below is a press release provided by the company/PR representative. It is published for informational purposes.
Kaspersky discovers new phishing campaign exploiting Google Tasks notifications to steal corporate credentials
February 26, 2026
Kaspersky has uncovered a new phishing scheme that abuses legitimate Google Tasks notifications to trick corporate users into revealing corporate login credentials. By leveraging Google’s trusted @google.com email domain and notification system, attackers bypass traditional email security filters and exploit users’ trust in familiar services.
In this campaign, victims receive an authentic-looking notification from Google Tasks with the subject line “You have a new task.” The message creates the illusion that the recipient’s company has adopted Google’s task management tool, pressuring them to act quickly. The notification often includes elements of urgency, such as a high-priority flag and a tight deadline, to prompt the victim’s immediate response.
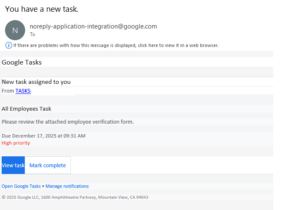 An email sent by the attackers via Google Tasks
An email sent by the attackers via Google Tasks
Upon clicking the embedded link, users are directed to a fraudulent form disguised as an “employee verification” page, where they are asked to enter their corporate credentials under the pretense of confirming their status. These stolen credentials can then be used for unauthorized access to company systems, data theft, or further attacks.
“Google’s vast ecosystem of services gets exploited by scammers. The scheme with Google Tasks is part of a broader trend observed before and continuing into 2026, where cybercriminals misuse legitimate platforms to distribute scams and phishing. Notifications originating from legitimate domains naturally evade many spam and phishing filters, while the social engineering aspect – making it seem like an internal company process – lowers the victim’s guard,” comments Roman Dedenok, Anti-Spam Expert at Kaspersky.
Read the article about this tactic on Kaspersky’s blog.
To counter this and similar threats, Kaspersky recommends:
- Treat unsolicited invitations from any platform with suspicion, even if they appear to come from trusted sources
- Carefully inspect URLs before clicking
- Do not call any phone numbers indicated in suspicious emails – if you need to call support of a certain service, it is best to find the phone number on the official webpage of this service
- Report suspicious emails to the platform provider and use multi-factor authentication for all accounts
- For corporate users, Kaspersky Security for Mail Server with its multi-layered defense mechanisms powered by machine learning algorithms provides robust protection against a wide range of evolving threats and offers peace of mind to businesses in the face of evolving cyber risks
- For individual users Kaspersky Premium offers AI-powered anti phishing features designed to help avoid phishing attacks and improve overall cybersecurity
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. With over a billion devices protected to date from emerging cyberthreats and targeted attacks, Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative solutions and services to protect individuals, businesses, critical infrastructure and governments around the globe. The company’s comprehensive security portfolio includes leading digital life protection for personal devices, specialized security products and services for companies, as well as Cyber Immune solutions to fight sophisticated and evolving digital threats. We help millions of individuals and nearly 200,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.
This article was originally published as Kaspersky Uncovers Google Tasks Phishing To Steal Credentials on Crypto Breaking News – your trusted source for crypto news, Bitcoin news, and blockchain updates.
You May Also Like

GOP lawmakers want nothing to do with Trump's ballroom chaos: report

Sustainable Fitch rates DBP’s sustainability bond framework as ‘good’






