Qualys Agent Val Redefines Cyber Risk Validation for CX Leaders
Qualys Agent Val: Redefining Risk Validation in the Age of Autonomous Security
The introduction of Qualys Agent Val marks a decisive shift in how enterprises approach cybersecurity execution. At a time when vulnerability volumes are accelerating and exploit timelines are shrinking, organizations are facing a structural inefficiency: they can identify risks at scale, but struggle to determine which ones actually matter.
Qualys Agent Val addresses this gap by moving beyond detection into validation and remediation. Instead of relying on theoretical severity scores, it enables organizations to test whether vulnerabilities can be exploited in real environments—and act accordingly. This transition from assumption-driven prioritization to evidence-based execution reflects a broader evolution in enterprise security strategy.
The Growing Intersection of Cybersecurity and Customer Experience
Customer expectations in digital ecosystems have evolved toward zero tolerance for disruption. Whether in financial services, e-commerce, or SaaS platforms, users expect uninterrupted access, secure interactions, and consistent performance. Any vulnerability that leads to downtime or compromise directly impacts trust and loyalty.
At the same time, enterprises are dealing with exponential growth in vulnerabilities and increasingly compressed exploit timelines. Attackers are no longer waiting for patch cycles; they are exploiting weaknesses as soon as—or even before—they are publicly disclosed.
This creates a critical pressure point for CX leaders. Security is no longer a backend concern—it is a determinant of customer experience quality. Failures in vulnerability management translate directly into degraded journeys, failed transactions, and reputational damage.
Strategic Shift: From Detection to Decision Intelligence
The launch of Qualys Agent Val reflects a deliberate strategic repositioning by . Rather than competing solely on visibility and detection, the company is focusing on decision intelligence—helping organizations act on risk with precision.
This is fundamentally an offensive move. By embedding exploit validation into its platform, Qualys is addressing a long-standing inefficiency: the gap between identifying vulnerabilities and resolving them effectively.
As Melinda Marks indicates in part, the industry is moving toward operational certainty through validation, rather than relying on descriptive metrics such as counts and severity scores.
The timing is significant. As exploit timelines shrink and engineering resources remain constrained, organizations need to ensure that every remediation action delivers measurable impact.
How Qualys Agent Val Works
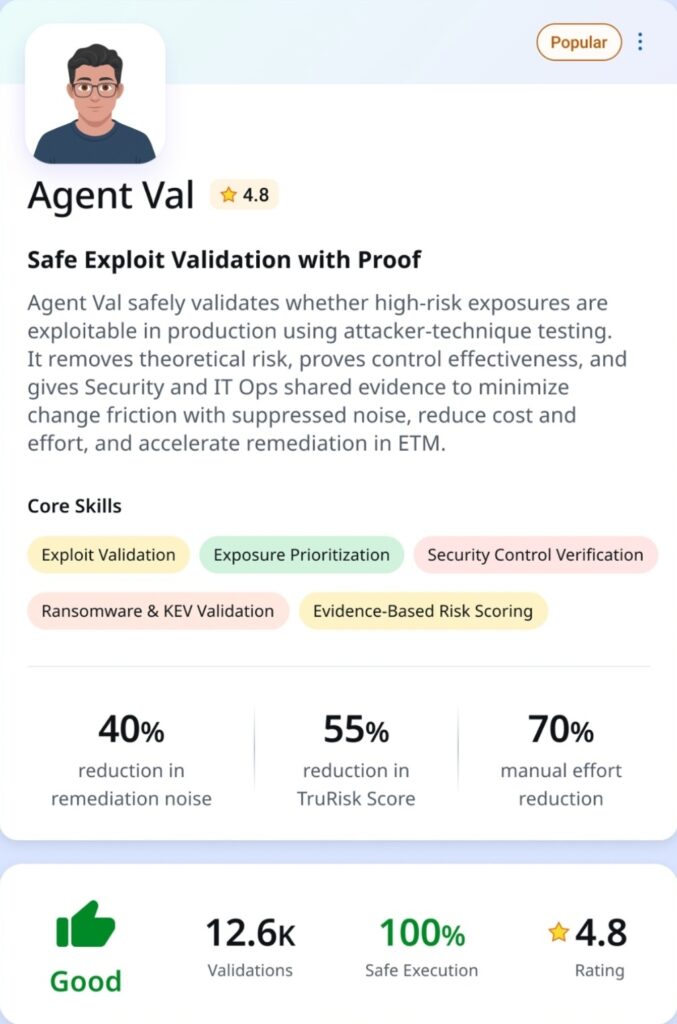
At its core, Qualys Agent Val functions as an AI-driven orchestration layer within the Enterprise TruRisk Management platform. Its primary role is to validate whether identified vulnerabilities can actually be exploited in a given environment.
The system analyzes multiple inputs, including exposure signals, asset criticality, and business context, to determine which vulnerabilities should be tested first. Using its TruConfirm capability, it safely simulates exploit scenarios in live environments to assess whether attack paths are viable.
Once validation is complete, the platform prioritizes remediation actions. These may include patching, compensating controls, or isolation strategies where patching is not immediately feasible. Crucially, the system then revalidates the environment post-remediation to confirm that the exploit path has been closed.
This closed-loop model differentiates Qualys Agent Val from legacy approaches that rely heavily on static scoring systems without execution-level verification.
Translating Security Efficiency into Customer Experience Gains
The operational efficiencies introduced by Qualys Agent Val have direct implications for customer experience. By reducing the time required to validate and remediate vulnerabilities, organizations can significantly improve system reliability and uptime.
From the customer’s perspective, this translates into fewer disruptions, more stable digital interactions, and increased confidence in platform security. Faster remediation cycles reduce the likelihood of incidents that could interrupt services or compromise data.
Additionally, the reduction in remediation noise—where teams focus only on exploitable vulnerabilities—enables engineering resources to be allocated more effectively. This leads to improved system performance and greater consistency in service delivery.
As Florian Bielak suggests in part, eliminating “noise” allows teams to focus on real-world risks rather than theoretical scenarios.
Industry Implications: Toward Autonomous Security Operations
The emergence of Qualys Agent Val highlights a broader structural shift in cybersecurity. The industry is moving from reactive models toward autonomous, AI-driven operations capable of continuous validation and remediation.
This evolution will raise expectations across the market. Vendors that focus solely on detection will face increasing pressure to incorporate validation and execution capabilities into their platforms.
More importantly, the definition of success in cybersecurity is changing. It is no longer about how many vulnerabilities are identified, but how effectively risk is reduced.
Future Outlook: Continuous Validation as the New Standard
Looking ahead, the principles underpinning Qualys Agent Val are likely to become foundational across enterprise security strategies. Continuous validation, contextual prioritization, and automated remediation will define the next generation of cybersecurity frameworks.
As Sumedh Thakar emphasizes in part, the key question is no longer whether a vulnerability exists, but whether it can actually be exploited in a specific environment.
For CX leaders, this shift has clear implications. Reliable, secure systems are essential to delivering consistent and trustworthy customer experiences. As cybersecurity becomes increasingly automated and intelligence-driven, its role in shaping customer journeys will only expand.
KEY TAKEAWAYS
- Exploit validation is replacing theoretical risk scoring
Organizations are moving away from severity-based prioritization toward evidence-based validation of real-world exploitability. - AI is evolving from analytics to autonomous execution
Solutions like Qualys Agent Val demonstrate how AI can directly drive remediation actions, not just insights. - Cybersecurity performance directly impacts customer experience
Faster and more accurate remediation reduces downtime, improves reliability, and strengthens customer trust. - Operational efficiency depends on intelligent prioritization
Eliminating remediation noise allows teams to focus on vulnerabilities that truly matter. - Continuous validation will define next-generation security models
One-time assessments are giving way to ongoing validation and revalidation as a standard practice.
The post Qualys Agent Val Redefines Cyber Risk Validation for CX Leaders appeared first on CX Quest.
You May Also Like
Aave DAO to Shut Down 50% of L2s While Doubling Down on GHO

New Crypto Investors Are Backing Layer Brett Over Dogecoin After Topping The Meme Coin Charts This Month


