Critical USDT0 Response to Drift Hack Exposes Stark Contrast in Stablecoin Security Protocols
BitcoinWorld
Critical USDT0 Response to Drift Hack Exposes Stark Contrast in Stablecoin Security Protocols
In a decisive security move that highlights evolving decentralized finance protocols, Tether’s unified liquidity protocol USDT0 responded to the Drift hack within 90 minutes by halting its cross-chain communication network on Solana. This rapid intervention, announced on March 15, 2025, through official channels, occurred as on-chain analyst ZachXBT revealed Circle had taken no comparable action despite millions in USDC moving through its Cross-Chain Transfer Protocol (CCTP) during the same incident.
USDT0 Protocol Executes Swift Security Response
Tether’s USDT0 protocol demonstrated remarkable operational efficiency during the Drift security incident. The unified liquidity platform immediately suspended cross-chain communication on the Solana network upon detecting anomalous activity. Consequently, this preventive measure potentially limited further exposure to the exploit. The protocol’s architecture, designed for rapid response capabilities, enabled security teams to implement network-level controls within the critical 90-minute window.
Furthermore, this incident represents a significant test for emerging cross-chain protocols. USDT0’s response mechanism, which involves automated monitoring and manual intervention protocols, functioned as intended during a live security event. The protocol’s ability to isolate specific network functions while maintaining overall system integrity provides valuable insights for the broader DeFi security landscape. Security experts note that such targeted responses represent an advancement over blanket shutdowns that can disrupt legitimate users.
Circle’s CCTP Protocol Faces Scrutiny
Meanwhile, Circle’s Cross-Chain Transfer Protocol (CCTP) operated without intervention during the same security incident. On-chain analyst ZachXBT documented substantial USDC movements through CCTP as the Drift exploit unfolded. This apparent inaction has sparked discussions about varying security philosophies among major stablecoin issuers. Circle’s protocol, which facilitates permissionless cross-chain transfers, presents different security considerations than more centralized alternatives.
Industry observers highlight the fundamental design differences between these protocols. USDT0 incorporates centralized control points for emergency response, while CCTP emphasizes decentralization and permissionless operation. These architectural choices directly influence response capabilities during security incidents. The table below illustrates key operational differences:
| Protocol Feature | USDT0 | Circle CCTP |
|---|---|---|
| Emergency Response Mechanism | Centralized control points | Decentralized validators |
| Response Time Demonstrated | 90 minutes | No intervention documented |
| Network Impact | Targeted function suspension | Full network operation |
| Security Philosophy | Active intervention capability | Permissionless operation priority |
Cross-Chain Security Implications
The Drift incident exposes critical considerations for cross-chain security architecture. Security researchers emphasize several key factors:
- Response Time Thresholds: The 90-minute benchmark establishes a new industry reference point
- Protocol Design Trade-offs: Centralized controls versus decentralized principles
- Communication Protocols: Transparency requirements during security events
- User Protection Mechanisms: How protocols safeguard end-user assets
These elements collectively shape how protocols balance security, decentralization, and usability. The incident particularly highlights the challenges of implementing security measures in permissionless environments where malicious actors can operate alongside legitimate users.
Solana Network Security Context
The Drift exploit occurred within the broader Solana ecosystem, which has experienced multiple security incidents throughout 2024 and early 2025. Solana’s high throughput and low transaction costs have made it attractive for DeFi applications but have also presented unique security challenges. The network’s architecture, which processes transactions rapidly across multiple parallel threads, creates complex security monitoring requirements.
Security analysts note that cross-chain bridges and communication layers represent particularly vulnerable points in blockchain ecosystems. These interfaces between different networks create additional attack surfaces that malicious actors can exploit. The Drift incident specifically involved manipulation of cross-chain communication, highlighting this persistent vulnerability category. Consequently, protocol developers increasingly focus on securing these critical junctures between blockchain networks.
Industry Response and Best Practices
Following the incident, several industry organizations have begun developing standardized response frameworks. These initiatives aim to establish:
- Clear communication protocols during security events
- Standardized response time expectations
- Cross-protocol coordination mechanisms
- Post-incident analysis and reporting standards
These efforts seek to balance the need for rapid response with the preservation of decentralized principles. The varying approaches demonstrated by USDT0 and CCTP during the Drift incident provide concrete case studies for these developing frameworks. Industry working groups are particularly interested in creating response protocols that maintain network integrity while addressing immediate threats.
Regulatory Considerations Emerging
The differential response to the Drift hack has attracted regulatory attention. Financial authorities in multiple jurisdictions are examining how decentralized protocols handle security incidents. Key regulatory questions include:
Protocol operators’ responsibilities during security events represent a developing area of regulatory focus. The contrast between USDT0’s active intervention and CCTP’s permissionless operation highlights fundamental questions about protocol governance. Regulatory bodies are particularly interested in how these approaches align with existing financial regulations and consumer protection standards.
Furthermore, cross-jurisdictional coordination presents additional complexity. Protocols operating across multiple legal frameworks must navigate varying regulatory expectations during security incidents. This complexity increases when protocols incorporate decentralized governance structures that distribute decision-making authority across global participant networks.
Conclusion
The USDT0 response to the Drift hack establishes important precedents for cross-chain security protocols. The 90-minute intervention demonstrates that rapid response mechanisms can function effectively within decentralized finance ecosystems. Meanwhile, Circle’s CCTP protocol operation during the same incident highlights the ongoing tension between security intervention and permissionless operation principles. These contrasting approaches will likely inform future protocol designs and regulatory frameworks as the industry continues maturing. The incident ultimately underscores that security response capabilities represent critical differentiators in the competitive stablecoin and cross-chain protocol landscape.
FAQs
Q1: What specific action did USDT0 take during the Drift hack?
USDT0 halted its cross-chain communication network on the Solana blockchain within 90 minutes of detecting the security incident, preventing potential further exploitation through its protocol.
Q2: How did Circle’s response differ from Tether’s during this incident?
Circle’s Cross-Chain Transfer Protocol (CCTP) continued operating without intervention during the Drift exploit, with millions in USDC moving through the protocol as documented by on-chain analyst ZachXBT.
Q3: What are the security implications of this differential response?
The contrast highlights fundamental design philosophies: USDT0 incorporates centralized control points for emergency response, while CCTP prioritizes permissionless operation and decentralization, creating different security and response capabilities.
Q4: Why are cross-chain protocols particularly vulnerable to exploits?
Cross-chain bridges and communication layers create additional attack surfaces between different blockchain networks, requiring complex security monitoring and presenting attractive targets for malicious actors.
Q5: What industry developments might follow this incident?
The event will likely accelerate development of standardized security response frameworks, clearer communication protocols during incidents, and more sophisticated cross-protocol coordination mechanisms for future security events.
This post Critical USDT0 Response to Drift Hack Exposes Stark Contrast in Stablecoin Security Protocols first appeared on BitcoinWorld.
추천 콘텐츠
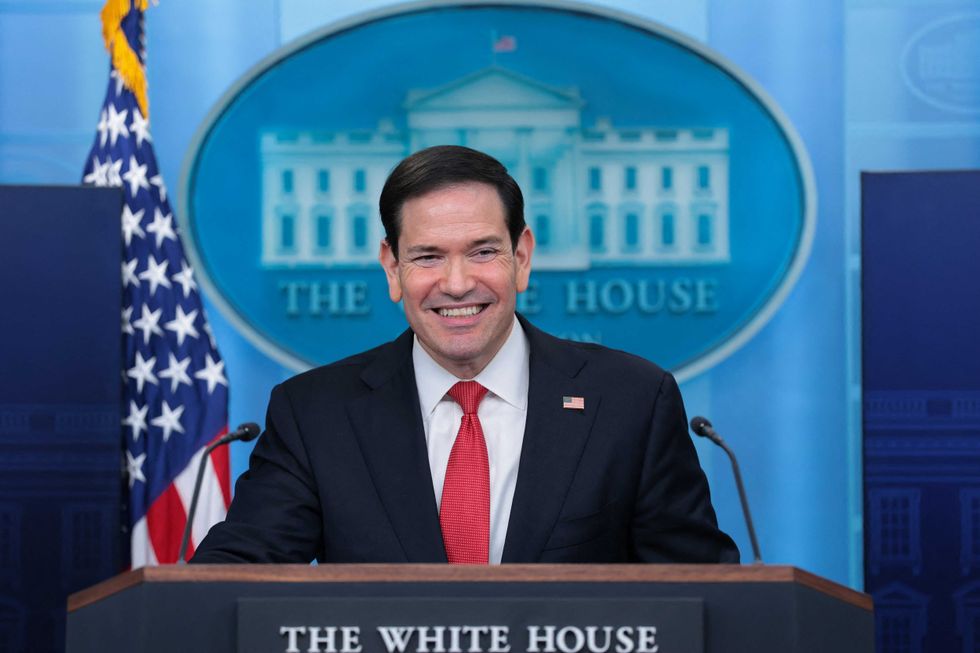
Rubio presidency would be an 'unmitigated disaster': conservative insider

DBP Q1 income up 26%






