Your Crypto Isn’t Safe Outside the Blockchain, Vitalik Buterin Warns
Ethereum co-founder Vitalik Buterin issued a stark reminder that while blockchain security prevents even a majority of validator collusion from stealing on-chain assets, this protection vanishes completely when users trust validators with off-chain tasks.
He noted that if 51% of validators collude or fall victim to software bugs, they cannot steal assets stored on-chain, but this ironclad protection vanishes the moment users trust validators with tasks beyond the blockchain’s direct control.
The warning particularly highlights a critical but often misunderstood boundary in blockchain architecture.
While on-chain funds remain cryptographically protected even under majority-attacker attacks, any off-chain activity that relies on validator honesty leaves users vulnerable to manipulation with no recourse.
The Security Boundary Blockchain Can’t Cross
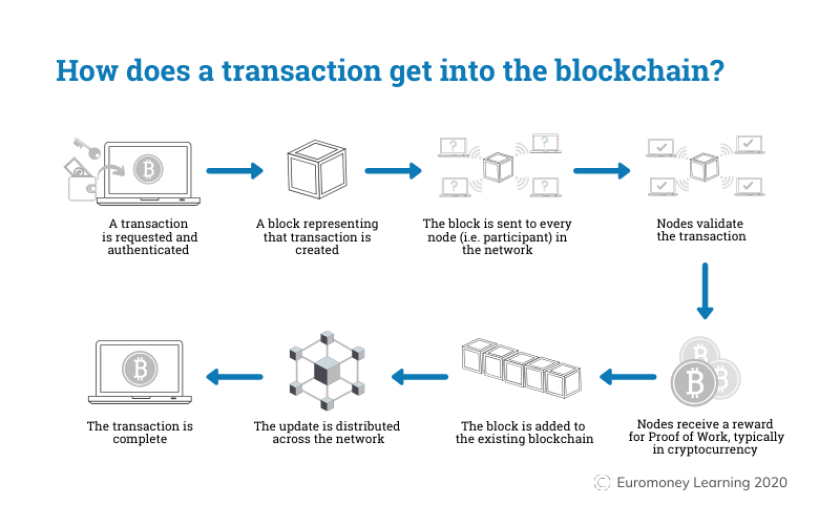
Blockchain protocols enforce strict validation rules that every node independently verifies by checking transaction signatures, preventing double-spending, and ensuring that state transitions follow the protocol logic.
This decentralized verification means colluding validators cannot forge transactions or create invalid blocks that steal user funds.
The system’s distributed nature ensures that even majority control cannot override these fundamental safeguards.
 Source: EMLearning
Source: EMLearning
However, this protection breaks down when validators handle off-chain tasks like oracle data feeds, governance decisions, or restaking services.
These activities fall outside the blockchain’s algorithmic enforcement and rely instead on validator honesty.
A colluding majority could provide false data or manipulated outcomes without the cryptographic proofs that protect on-chain transactions.
Users affected by such off-chain collusion have no automatic dispute-resolution or recovery mechanism.
The blockchain cannot verify or contest decisions made beyond its consensus layer, leaving victims without the recourse that makes on-chain assets fundamentally secure.
Why Off-Chain Trust Amplifies Risk
Traditional blockchain verification requires computers to perform 100 times as much work as the original calculation.
However, when users move funds off-chain, through custodial wallets, centralized exchanges, or validator-controlled computations, they surrender the blockchain’s built-in protections.
Off-chain systems lack the independent verification that every on-chain node provides, leaving them vulnerable to majority validator manipulation.
The distinction matters because blockchain consensus operates through algorithmic rule enforcement that no single party controls.
Off-chain activities depend on coordinated behavior and validator integrity, but not on protocol-level verification.
Smart contracts that rely on validator-provided oracle data could yield incorrect outcomes if a majority colludes to report false information, potentially causing financial losses that on-chain mechanisms cannot prevent or reverse.
When asked whether his warning referenced restaking protocols like EigenLayer, Buterin confirmed the platform addresses this vulnerability through slashing mechanisms using its own token.
This economic penalty system provides some protection but cannot match the cryptographic guarantees that secure on-chain block validity against majority attacks.
Balancing Privacy with Blockchain’s Transparency Shield
Buterin’s security reminder comes as Ethereum pursues major privacy improvements that are different from the network’s traditionally transparent nature.
Earlier this month, he detailed GKR, a cryptographic technique that verifies calculations 10 times faster than traditional methods while enabling zero-knowledge proofs, allowing computers to prove calculations are correct without revealing the underlying data.
The Ethereum Foundation also launched a 47-member Privacy Cluster in September to make network privacy default rather than optional, addressing concerns that public blockchains expose too much financial information.
Aside from enterprise demand, Vitalik sees it as the only way to global adoption, especially for Ethereum.
Just recently, while speaking with Cryptonews, industry expert Petro Golovko compared current blockchain transparency to the pre-encryption internet era, arguing that systems exposing salaries and account balances remain “unusable for regular people and impossible for institutions.”
The initiative aims to enable private transactions, selective identity disclosure, and improved user privacy experience without sacrificing the verification mechanisms that prevent validator manipulation.
However, the privacy push creates an apparent paradox. If transactions become private, how can the network maintain the transparent verification that protects against off-chain manipulation, Buterin warned about?
The solution lies in cryptographic techniques like GKR that allow verification of transaction validity without exposing transaction details, preserving the blockchain’s core security property where invalid blocks remain rejected even under majority attacks, while shielding sensitive financial data from public view.
추천 콘텐츠

Solana Remains Above Its $75 Support Level

68% of global BTC miners came from the U.S., Russia, and China, Q1 2026






