Firefox finds 20 year old bug and patches 14 months of fixes in 30 days using Anthropic’s Mythos AI
Mozilla’s latest Firefox security update provides a rare glimpse into what happens when frontier AI capabilities reach defenders before attackers. The company said it fixed 423 Firefox security bugs in April after gaining access to Claude Mythos Preview, compared with roughly 420 fixes over the previous 14 months.
That compression is the signal.
The defensive side did in one month what had previously taken more than a year, then disclosed a sample of the bugs to show the depth of latent risk still present inside a mature, heavily tested browser codebase.
The strongest anchor is age.
One of the disclosed bugs, Bug 2025977, was a 20-year-old XSLT reentrancy issue in which key() calls could trigger a hash table rehash, free backing storage, and leave a raw entry pointer in use. Another, Bug 2024437, involved a 15-year-old flaw in the HTML <legend> element.
These are exactly the kinds of long-buried defects that can survive ordinary testing, fuzzing, and manual review because they sit inside obscure edge cases, older subsystems, or complex interactions across distant parts of the browser.
Mozilla said Claude Mythos Preview helped identify and fix 271 bugs in the Firefox 150 release, with additional fixes shipped in 149.0.2, 150.0.1, and 150.0.2. Of those 271 Firefox 150 bugs, 180 were rated sec-high, 80 were sec-moderate, and 11 were sec-low.
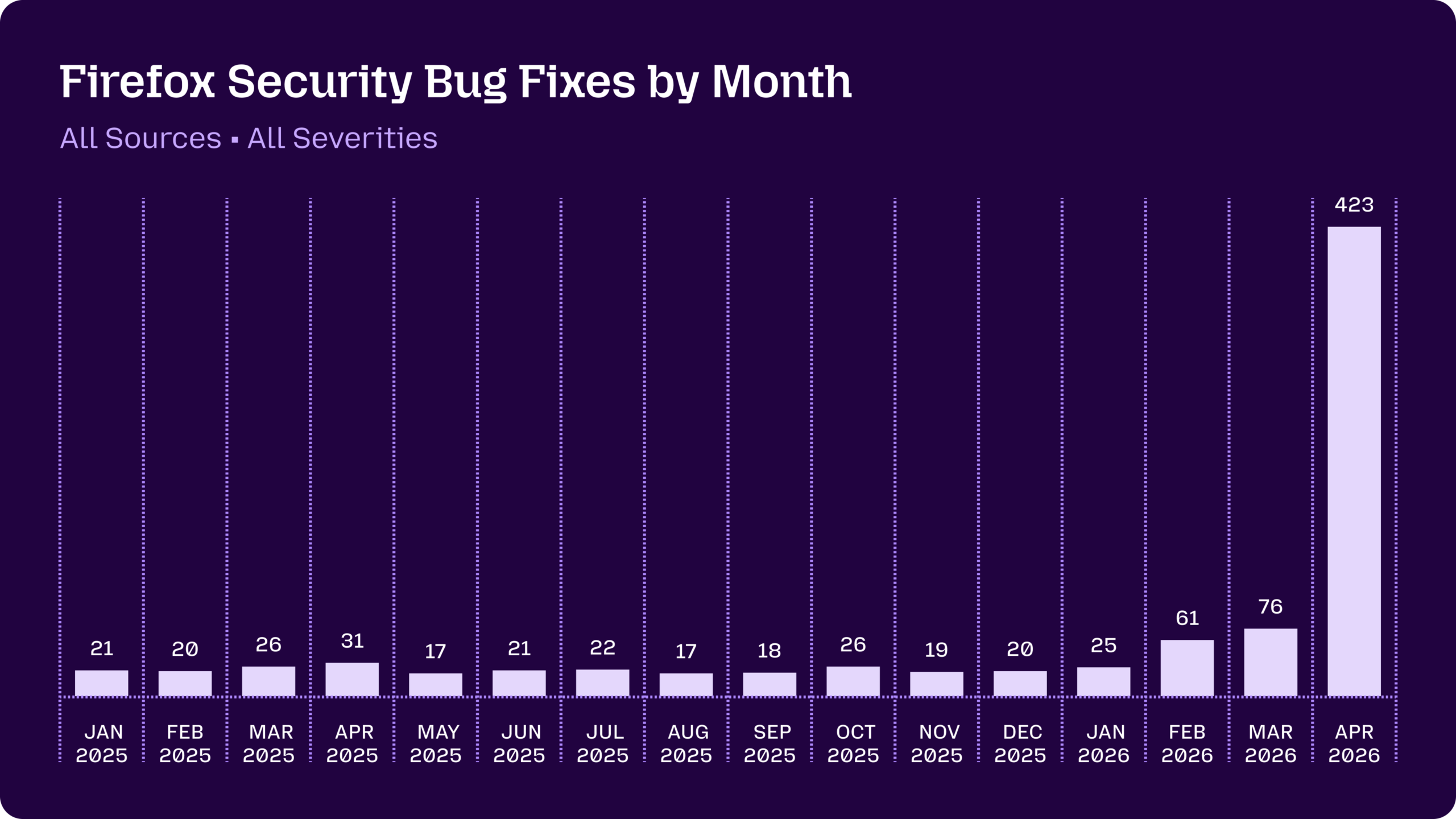 A graph showing the volume of Firefox security bug fixes shipped by month, trending in the 20-30 range throughout each month in 2025, with a spike to 60-70 in February and March 2026, up to 423 in April 2026
A graph showing the volume of Firefox security bug fixes shipped by month, trending in the 20-30 range throughout each month in 2025, with a spike to 60-70 in February and March 2026, up to 423 in April 2026
Mozilla’s security severity framework assigns sec-high to vulnerabilities that can be triggered by normal user behavior, such as visiting a web page. That places the findings in a serious operational category, even where Mozilla had built no full proof of real-world weaponization.
The 20-year bug shows how long exploitable-looking flaws can survive
Firefox is an old, high-value, heavily scrutinized browser. Its code has been tested by internal teams, external researchers, fuzzers, bug bounty hunters, and attackers for years.
That makes the April surge more important because the vulnerabilities surfaced inside a project with mature security engineering rather than inside a lightly reviewed codebase. Mozilla said AI-generated security reports to open-source projects had previously carried a high noise burden for maintainers.
Reports could look plausible while still being wrong, and the asymmetry was obvious: generating claims was cheap, while validating them consumed experienced engineering time.
The dynamic shifted as models improved and Mozilla built a harness around them. The company described a pipeline that could steer models toward specific code areas, generate reproducible test cases, filter noise, deduplicate findings, triage severity, and move confirmed bugs into the security lifecycle.
That surrounding system is central to the result.
The model provided discovery power, while the harness turned that power into confirmed reports and patches.
The disclosed sample in Mozilla’s technical write-up included a WebAssembly GC bug that could create a fake-object primitive with potential arbitrary read or write, IPC race conditions affecting parent-process reference counts, raw NaN deserialization across an IPC boundary, parent-process stack memory leakage during DNS parsing, use-after-free flaws, and sandbox escape candidates.
These are security primitives that attackers value because they can become parts of exploit chains. A memory corruption bug can become a foothold.
An information leak can improve reliability. A sandbox escape can expand control from a constrained process into a privileged one.
The 20-year-old XSLT issue sharpens the implication.
A bug can persist across multiple generations of browser architecture, testing practices, and security staffing. Longevity does not automatically create exploitability, but it does create time for discovery and refinement by anyone capable of finding it.
A hostile actor with Mythos-level tooling before Mozilla’s April patch run would have had a larger search surface, a better way to generate proof-of-concept exploits, and a stronger chance of finding old flaws that had escaped previous methods.
Mozilla also emphasized that several bugs were sandbox escapes. That category requires precision.
A sandbox escape usually assumes that a content process has already been compromised, then uses another vulnerability to reach a more privileged process. In browser exploitation, this is a critical layer.
A first-stage bug can place attacker-controlled code inside a constrained rendering process. A second-stage sandbox escape can move execution toward the browser’s parent process, where the attacker has far more leverage.
From there, the attacker may try to access browser-mediated data, manipulate web sessions, observe sensitive activity, or pivot into additional device-level exploitation depending on operating-system defenses, permissions, and chain reliability.
The worst case is attacker-first access to Mythos-level discovery
The central risk is access sequencing.
Mozilla discovered a Mythos-level vulnerability before a hostile actor used the same class of model-assisted pipeline against Firefox at scale. Reverse that order, and the security picture changes.
A company facing attackers with earlier access to these systems would be defending against a faster search process, a deeper exploit inventory, and a larger pool of chainable primitives. The sharp risk is that a sophisticated actor can use model-driven auditing to locate entry bugs, information leaks, sandbox escapes, and reliability aids across the same target before maintainers can identify, triage, patch, test, and ship fixes.
A realistic high-end attack chain would use several pieces.
The first piece is a trigger that can be reached through ordinary browsing. Mozilla’s own severity framework says sec-high bugs can be triggered by normal user behavior, including visiting a page.
The attacker then needs a primitive that gives code execution or memory corruption inside a sandboxed content process. A JIT, WebAssembly, layout, DOM, or parsing bug can serve that role if it can be made reliable.
The next piece is a leak or type confusion that helps defeat address-space layout randomization or improves memory shaping. The third piece is a sandbox escape, such as a parent-process race, IPC boundary confusion, or privileged decoding path.
The final layer is post-exploitation code that turns browser control into useful access.
That end state is severe.
A successful full-chain browser compromise can expose whatever the browser can see or mediate. For ordinary users, that can include active web sessions, sensitive page content, credentials entered into sites, browser-accessible files exposed through permissions, and the ability to manipulate pages in ways that alter what a victim sees.
For crypto users, the risk profile is sharper.
Browsers sit between users and exchanges, wallets, bridges, portfolio tools, token approvals, custody dashboards, and internal admin panels. A browser-level compromise against a targeted crypto user could attempt to hijack sessions, alter transaction details before signing, inject malicious wallet prompts, capture credentials during entry, or use the browser as a foothold for deeper compromise against a trading desk, developer machine, journalist, or exchange employee.
The most dangerous version is targeted rather than mass-market.
A nation-state, ransomware affiliate, or financially motivated group would likely avoid noisy broad exploitation at first. It could compromise websites likely to be visited by a narrow target set, send tailored links, or use a watering-hole campaign against developers, crypto executives, validators, researchers, infrastructure operators, or newsroom staff.
The victim only needs to browse to the wrong page if the chain is reliable enough and the target’s Firefox build remains vulnerable. Mozilla notes that many sandbox escapes require an already-compromised content process, which defines the attacker’s assembly problem.
Mythos-level capability helps search for exactly those missing chain links.
The attacker’s advantage comes from scale and optionality.
Traditional exploit research requires scarce expertise, deep target knowledge, and time. Model-assisted security harnesses can reduce the search cost.
They can inspect more files, test more hypotheses, and generate more reproducible cases than a small human team alone. A sophisticated human still has to guide, validate, and weaponize the results.
The model compresses the discovery phase and expands the menu of candidate bugs. For defenders, patch velocity becomes a strategic constraint.
For attackers, the prize is a period in which their discovery curve moves faster than the company’s remediation curve.
Crypto users sit close to the blast radius of browser compromise
For the crypto industry, browser security is an upstream risk.
Wallets, exchanges, bridges, analytics dashboards, custody portals, governance tools, and internal admin panels all depend on the browser as a trust boundary. A secure signing flow can be weakened by a compromised browser environment.
A protected exchange account can be exposed through a hijacked session or a manipulated interface. A newsroom, developer team, or fund can be targeted through ordinary web activity and then pressured through credential theft, session abuse, or transaction manipulation.
A hostile actor with early access to Mythos-level capability would gain an advantage in the reconnaissance phase.
The attacker could direct the system toward browser subsystems that interact with web content, serialization, media parsing, graphics, IPC, DNS, image decoding, permissions, or privileged process boundaries. Each confirmed defect would become a candidate building block.
Some candidates would fail. Others would require unusual victim behavior.
A smaller set could become operational when paired with other bugs. That funnel is enough to create serious risk when the target population includes high-value wallets, exchange operators, infrastructure engineers, or journalists covering sensitive markets.
The danger also extends to supply-chain and operational workflows.
Crypto teams often rely on browser-based admin consoles for cloud providers, analytics services, customer support systems, exchange dashboards, hardware wallet interfaces, treasury tooling, and communications platforms. A browser-level exploit against a single privileged employee could place the attacker inside systems that were never directly vulnerable.
In that scenario, the browser becomes the bridge between public web content and private operational access.
Mozilla’s April patch surge should therefore be treated as an early warning for the broader software stack.
The company had the model, the harness, and the engineering capacity to convert findings into fixes. Many companies have only part of that system.
Some have no comparable pipeline at all. If attackers receive equivalent discovery capability first, the gap between latent bugs and operational exploitation can shrink.
The defensive side then faces compressed timelines across validation, patching, regression testing, disclosure, and user updates.
Mozilla’s own FAQ adds an important boundary.
A sec-high or sec-critical bug is not automatically equivalent to a practical exploit. In many cases, a single bug is insufficient for full Firefox compromise because the browser has a defense-in-depth architecture, sandboxing, site-specific processes, and operating-system mitigations such as ASLR.
Mozilla also said it generally does not build exploits to determine whether each bug could be used by an attacker in the real world. It classifies high-severity issues based on dangerous symptoms such as use-after-free or out-of-bounds memory behavior and assumes that any such issue may be exploitable with enough effort.
That conservative posture is appropriate because false negatives in exploitability analysis are costly.
Defenders need model-assisted auditing before attackers industrialize it
Mozilla’s work points toward a new security threshold for major software projects.
Access to advanced models is only one layer. The organization also needs a system that turns findings into shipped fixes without collapsing under volume.
The company described the operational burden clearly: every bug required care, attention, review, testing, and release management. More than 100 people contributed code to the hardening effort, alongside engineers working on triage, scaling, testing, and releases.
The model increased discovery throughput, and the organization had to absorb the resulting patch load.
The same dynamic applies beyond browsers.
Any company with a large codebase, a complex permission model, or an exposed parsing surface faces a discovery environment that can change quickly when a more capable model becomes available. Exchanges, wallet providers, custody platforms, payment processors, identity systems, cloud services, and developer tooling companies all share the same structural problem.
Attackers can point models at old code, low-traffic modules, awkward boundary layers, serialization formats, plugin systems, parsers, and privilege transitions. Those are the places where old assumptions accumulate and where exploit-chain components often sit.
Mozilla’s example also shows why prior hardening investments can pay off under model pressure.
The company said its models attempted sandbox escapes via prototype pollution in the privileged parent process, but those attempts were blocked by an earlier architectural change that froze prototypes by default. AI-assisted discovery increases pressure on weak seams.
Strong defaults, privilege separation, sandboxing, memory safety, fuzzing, and exploit mitigations can force attackers into longer chains. Longer chains increase cost and failure points.
When frontier models make vulnerability discovery cheaper, architectural defenses become more valuable because they turn isolated bugs into incomplete attacks.
The policy debate around frontier security models often centers on offensive or defensive use.
Mozilla’s case shows the answer depends on who gets access first and who has the operational capacity to act on the output. In defender hands, Mythos-level systems can accelerate hardening.
In the attacker's hands, the same class of capability can accelerate inventory building. The asymmetry is practical.
Attackers need fewer confirmed results, can keep findings private, and can focus on a narrow target. Defenders need to fix broadly, avoid regressions, coordinate releases, and protect slow-updating users.
That leaves companies with a direct mandate: build AI-assisted security pipelines before adversaries use comparable systems against them.
The next phase of vulnerability management will favor teams that can scan continuously, reproduce findings automatically, route reports intelligently, and ship patches quickly. Mozilla said it intends to move toward continuous integration scanning as patches land in the tree.
That is the correct direction.
The window between discovery and exploitation is narrowing. Companies with model access, harness maturity, and release discipline will reduce latent risk.
Companies waiting for public advisories may learn about their own bugs after someone else has already turned them into infrastructure.
Mozilla’s April patch surge shows that the defender advantage is still possible when access, tooling, and release capacity align.
The same episode also shows how fragile that advantage can be. A 20-year-old bug was still present.
Sandbox escape candidates were still present. Hundreds of security fixes moved through the pipeline in one month after model-assisted discovery scaled.
The next test is whether the rest of the software ecosystem builds comparable defensive capacity before Mythos-level vulnerability discovery becomes routine in offensive hands.
The post Firefox finds 20 year old bug and patches 14 months of fixes in 30 days using Anthropic’s Mythos AI appeared first on CryptoSlate.
You May Also Like

Strategy CEO Highlights Scenarios Where Company Would Sell Bitcoin — Report

Scott Jennings accused of 'cheating' as fiery exchange breaks out on CNN: 'Let me finish!'






